
Information security protocols are only as effective as your team’s execution. In 2026, the requirements for protecting sensitive data have changed, forcing you to move beyond basic maintenance.
You need to define a resilient security posture that satisfies both technical requirements and legal scrutiny.
The current cybersecurity landscape requires you to abandon high-level theory. That means prioritizing the latest cybersecurity topics that define the industry today.
Highlights
Cybersecurity rarely sits still. Every year brings a fresh batch of tools, tactics, and attack methods that force security teams to rethink how systems are designed and defended.
In 2026, the challenge comes from two directions at once. On one side, emerging technologies are transforming how companies build and run software.
On the other hand, attackers are adapting just as quickly, probing every corner of modern digital infrastructure for weaknesses.
Some key trends to keep in mind:
For you and your team, the security conversation has moved past simple firewalls and antivirus tools. You’re now managing
That’s why cybersecurity topics and documentation have become more strategic than they used to be.
When you provide clear breakdowns of your architecture, security controls, and operational procedures, you enable your team to respond to incidents faster.
This is the only way to manage the cybersecurity challenges inherent in today’s hyper-connected environments.
The cybersecurity landscape looks different from even a few years ago. Organizations now run complex cloud systems, connect thousands of devices, and rely on automation across their digital infrastructure.
These changes improve efficiency, but they also increase exposure to cyber threats and operational security risks.
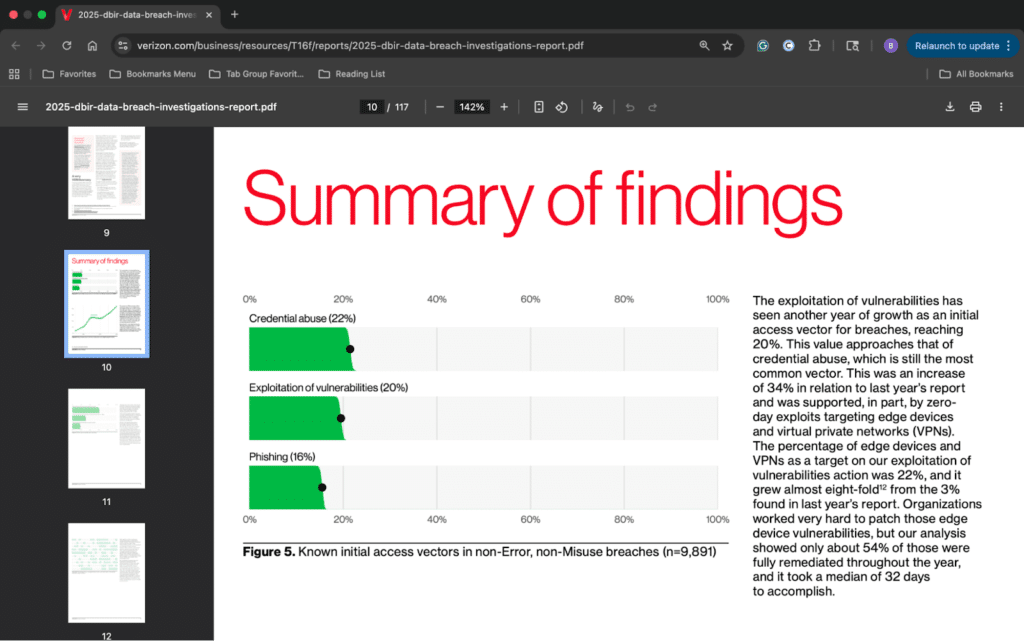
At the same time, attackers have become more organized. Many operate as professional cybercrime groups that specialize in ransomware, credential theft, and large-scale data breaches.
Because of this, security teams focus on stronger cyber defense strategies and more risk management practices.
Let’s look at some key cybersecurity topics that recur in modern security architecture.
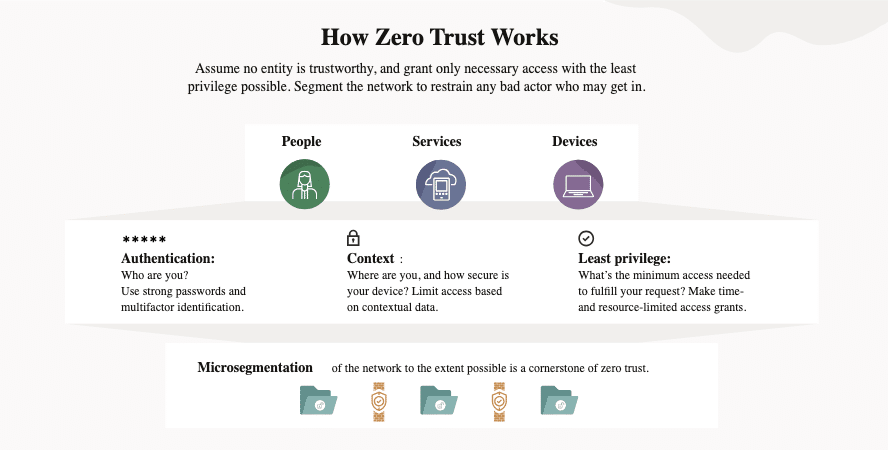
Zero-trust architecture sounds dramatic, but the idea is simple: stop assuming anything deserves trust.
In older security models, systems trusted activity inside the network. If someone logged in through the VPN, they often moved around freely.
Zero-trust architecture ends that idea.
Each request must prove its identity. Systems check identity, device health, and user role before access.
A typical zero-trust architecture uses multi-factor login, identity tokens, and strict access rules. APIs verify those tokens each time a service requests data.
This reduces the damage attackers can cause once they gain access. Many cyberattacks begin with stolen credentials or credential stuffing that exploits reused passwords.
Zero-trust limits how far attackers can move once they enter a system.
Security teams also pair zero-trust models with strong cyber hygiene practices. These include identity monitoring, password policies, and access audits. With these controls, businesses reduce the risk of an insider threat or unauthorized privilege escalation.
Security guides often explain these identity flows. Writers document login checks, token use, and access rules. Logs track every login and access attempt. This supports cyber incident reporting if suspicious activity appears.
In short, zero trust security treats every request as a risk until proven safe, relying on strict access controls, identity and access management, and multi-factor authentication to validate every interaction.
For technical writers, this changes the nature of the documentation job itself. You’re no longer describing access in broad system terms. You need to specify who can access what, under which conditions, and what evidence the system records at each step.
That means login flows, token validation rules, device checks, and privilege boundaries all need enough precision that engineers, auditors, and incident responders can pull from the same source of truth.
Most encryption today relies on math that modern computers can solve quickly.
Quantum computers could change that.
Large quantum machines may break some current encryption methods. Because of this risk, researchers now work on quantum-resistant encryption.
These systems rely on math problems that remain hard even for quantum machines.
Government and tech firms now test quantum-resistant encryption for future systems. Some security plans already include it. These are usually organizations that handle sensitive data. Think financial systems, healthcare records, and national critical infrastructure. They often begin preparing early.
Security planning also relies on guidance from frameworks developed by the National Institute of Standards and Technology.
These frameworks help security teams strengthen information security practices and prepare for future threats.
Technical writers might see new crypto tools, new key exchange methods, and new security libraries. Many systems now test hybrid models that mix current encryption with quantum-resistant encryption.
The goal is simple. Protect data that must stay safe for years.
Security teams rely on data to spot attacks.
Every login, file request, and API call creates a record. These records appear in threat detection logs.
These logs track user interactions, system events, and access attempts. Security tools scan them to spot strange behavior.
For example, a login at an odd hour or from a new country might raise a flag. Large data transfers or unusual administrative actions may signal an active breach.
Threat detection logs also support cybercrime investigations. They help analysts reconstruct the sequence of events during data breaches or other security incidents.
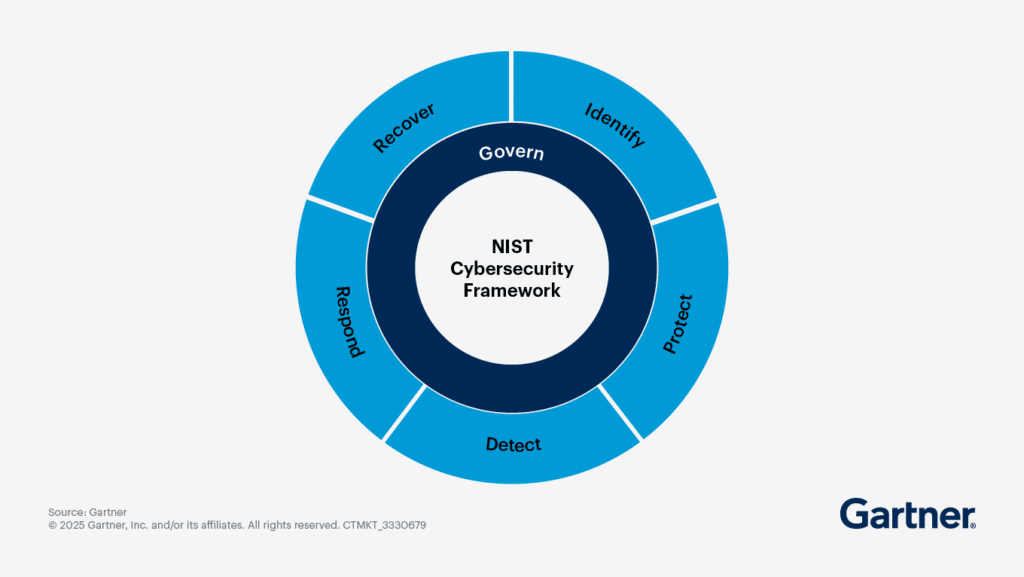
Many organizations structure their monitoring programs around the NIST Cybersecurity Framework. This is a framework that provides guidance on detection, response, and recovery.
Government agencies, such as the Cybersecurity and Infrastructure Security Agency, are also important. They encourage organizations to implement faster cyber incident response reporting. This helps to improve monitoring and strengthen cybersecurity resilience.
Technical guides often explain how systems create threat detection logs. Writers describe event types, time stamps, and log formats.
They also document how logs move into monitoring tools that watch for threats.
When a breach occurs, threat detection logs help teams rebuild the timeline.
AI tools bring new risks. Many organizations now rely on artificial intelligence. They use tools like generative AI systems and AI chatbots to automate tasks, answer questions, and assist developers.
These systems often connect to internal data sources, APIs, or enterprise tools. That access introduces new cyber risks.
Bad actors can manipulate large language models (LLMs) through prompt injection attacks. They craft input designed to trick models into revealing sensitive data or running unauthorized commands.
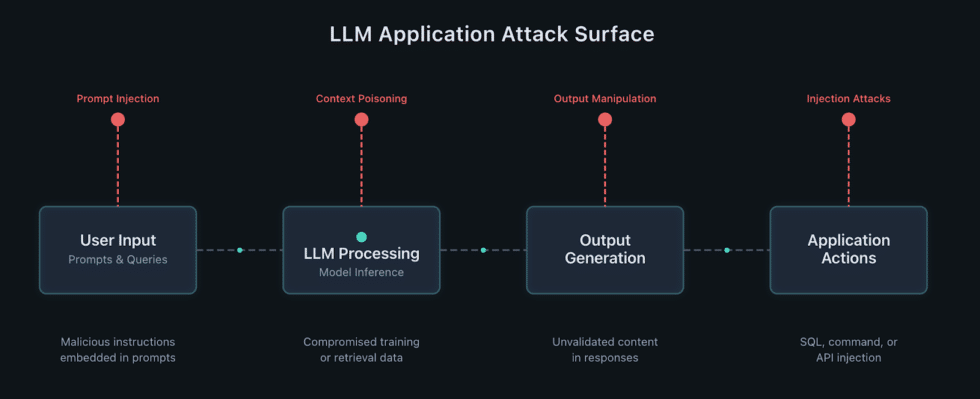
AI systems may also generate insecure code or expose hidden system behavior if proper safeguards are missing.
Because of this, LLM security has become a major focus for security teams. Organizations now implement guardrails that filter prompts, limit tool access, and monitor how AI agents interact with systems.
Technical documentation explains these controls. Writers often describe measures like:
Security teams also monitor AI interactions across cloud systems to prevent the spread of malicious code or unauthorized data exposure.
Teams also track model use to spot abuse.
For writers, the key shift is this: feature descriptions aren’t enough anymore. You need to state which systems the model can access, what actions it can trigger, what input gets filtered, what output gets logged, and who reviews exceptions.
Without that detail, teams can’t consistently test controls or investigate misuse.
AI might help teams work faster. But it can also expose data if safeguards are missing.
Identity fraud has grown more complex. Attackers now create fake people using real data mixed with false details. This method creates synthetic identities that can pass many traditional verification checks.
These accounts may open financial accounts, bypass authentication systems, or gain access to online services.
At the same time, deepfake technology allows attackers to create realistic voices, videos, and images.
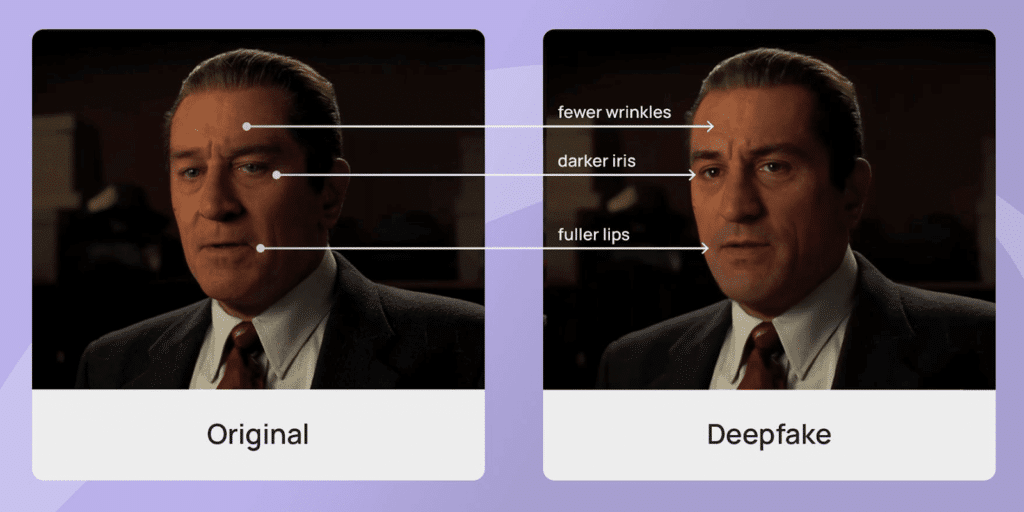
These tools can allow advanced social engineering attacks.
For example, a fake voice recording of an executive could trick employees into transferring money or sharing sensitive information.
Many scams now start on social media, where fake accounts build credibility before launching attacks, which is why teams often rely on a phishing simulation guide to train employees to recognize and respond to these tactics.
To counter these threats, organizations can use stronger identity verification systems. These systems analyze biometric signals, device fingerprints, and behavior patterns. You can now use TruthScan, which provides comprehensive AI detection across text, images, voice, and video, helping organizations safeguard themselves against increasingly sophisticated AI-generated threats.
Many cybersecurity topics in 2026 focus on how teams build, test, and monitor systems.
As a technical writer, you document the controls and processes that help teams stop attacks and manage risk.
Below, we cover the most common requirements.
Writers documenting secure development practices should be familiar with Static Application Security Testing (SAST), which analyzes source code early in the lifecycle to identify vulnerabilities.
Explaining how SAST fits into the broader security workflow helps teams understand prevention rather than just remediation. Clear documentation ensures these practices are consistently applied across projects.
Security frameworks can be tricky to write about because some of them describe a process rather than a product, and that difference is easy to miss if you’re not careful. Continuous threat exposure management is a good example of this. It’s a five-stage cycle that security teams use to find, rank, and fix weaknesses across their systems on an ongoing basis, not just once a year.
Gartner introduced it as a strategic program, so when it appears in documentation or articles, it shouldn’t be described as a piece of software you can just download and run.
The five stages, scoping, discovery, prioritization, validation, and mobilization, feed into each other in a loop, and that looping structure is actually worth explaining to readers because it changes how the whole thing works.
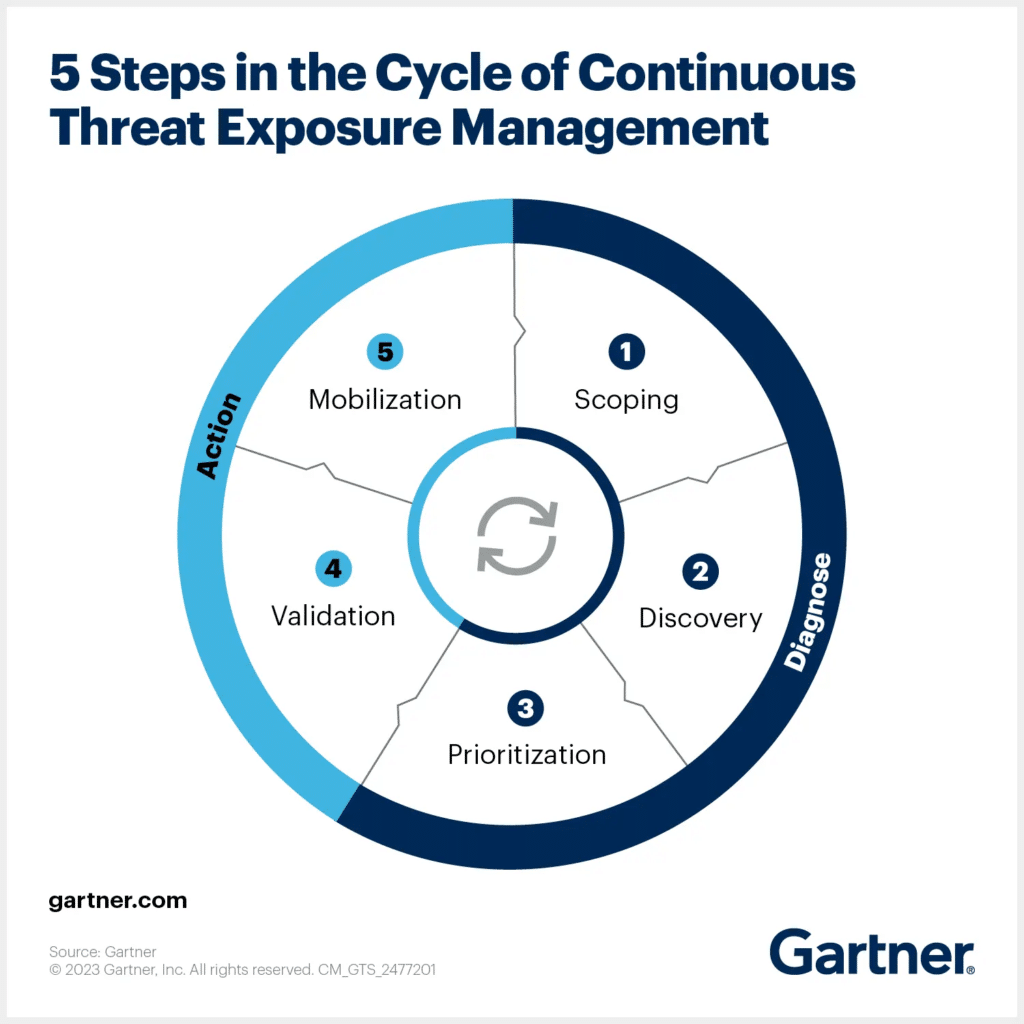
Keeping that process-focused framing in mind will make the writing more accurate and easier for both technical and general audiences to follow.
AI tools help developers write code faster. But they can also produce weak logic, insecure defaults, or unsafe patterns.
That’s why documentation needs to cover how teams review, test, and approve AI-generated code before it ships. Give developers a clear process, and they’ll catch problems early, before those problems catch you.
Many attacks begin with stolen login data. Because of this, identity checks sit at the center of modern security. Systems must verify users, devices, and access levels before granting entry.
Your documentation should clearly explain authentication steps and access rules.
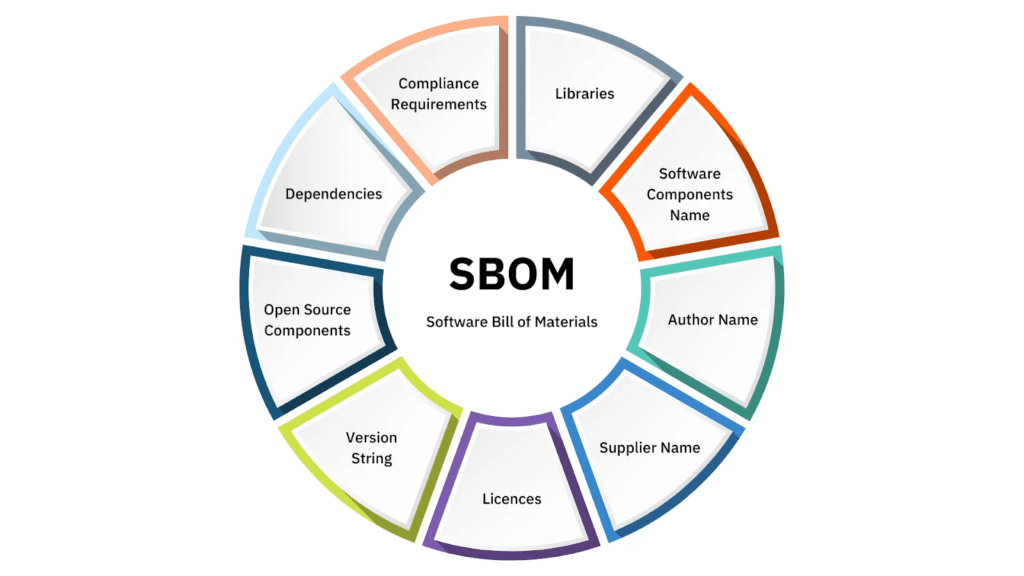
Most software depends on third-party code.
An SBOM lists every component in an application. It helps teams track dependencies and respond faster to vulnerabilities.
Explain how your team generates and reviews SBOMs. That means covering how vulnerabilities get identified, how affected components map back to specific systems, and how teams decide whether to patch, isolate, or replace a dependency.
Many laws now control where data can live.
You must document where data is stored and how it moves across systems. Clear records keep your team compliant. But they also help you trace data movement across regions, spot unauthorized transfers, and move fast when a regulatory audit lands.
Your security program must prove its defenses work.
Continuous monitoring and testing help teams detect problems early. Your documentation should explain how systems log events and report incidents.
Cybersecurity will keep evolving. New tools will appear. Attackers will adapt. Systems will grow more complex.
Your cybersecurity topics and documentation must keep up.
Clear guides help your team act fast during an incident. Engineers understand how systems work. Security teams know where to look and what to do.
Publishing those updates quickly matters just as much as writing them.
With Wordable, you can move documentation from draft to your CMS in seconds. You reduce manual formatting, avoid copy-paste errors, and keep critical updates live across your content.
Stop manual formatting. Your security updates shouldn’t wait on a slow publishing process.